How to Use Crypto Anonymously (Part 2)
This practical guide shows you exactly how to become anonymous while using crypto. Break the link to your identity with proven tools and step-by-step methods.

Bottom Line: One‑Minute Summary
Privacy means you control what you reveal, when, and to whom. But on a transparent blockchain, mandatory Know Your Customer (KYC) checks tie your holdings to your identity, leaving you no choice. Governments, data brokers, hackers, and criminals likely already know your balances. If you are lucky, they do not know yet, but one more data breach in the constant stream of hacks exposes your entire financial history. You can recover control. But anonymizing your holdings requires operational discipline, and the right methods.
Bitcoin: The Monero Bridge
Bitcoin has no on-chain privacy. The only robust playbook is conversion. Exit Bitcoin to Monero via atomic swaps (Eigenwallet, ~2% markup, fastest) or P2P markets (Bisq or Retoswap, 1.3% to 2.5% fees, better liquidity). Churn inside Monero for days or weeks, then swap back to fresh Bitcoin wallets using different tools than your exit. Coordinators can correlate metadata even when the chain looks clean. Time and tool separation are essential to break that correlation. This costs 4% to 5% and requires four weeks of operational discipline.
Ethereum: Shield On-Chain
Railgun is the balanced choice for good actors needing future compliance. It enables private DeFi through shielded addresses for 0.5% total (0.25% each way), offers substantial anonymity sets ($36 million), and provides Proof of Innocence to verify clean funds without revealing history. Privacy Pools offers the simplest user experience, excluding illicit funds through automated compliance checks for 0.5% entry fees, though its low $1.5 million anonymity set increases correlation risk. Tornado Cash remains the cypherpunk standard. Immutable and permissionless, it offers the largest anonymity set ($400 million+) and lowest fees (0.3%). By mixing with all funds including illicit, you permanently detach from regulated finance, centralized stablecoins, and CEXs, requiring private off-ramps if you plan to transfer crypto back to fiat.
The Cost Structure
Ethereum privacy costs 0.5% and takes two to three weeks. Bitcoin anonymization costs 4% to 5% and requires four weeks.
Read on for detailed comparisons and step-by-step execution playbooks.
The KYC Trap
You have six or seven figures sitting on Coinbase or Kraken. You've finally confronted the truth: Not your keys, not your crypto. Worse, that custodial convenience has become a direct liability. Governments have a history of debanking founders and freezing accounts under political pressure. Agencies like the FBI and NSA have repeatedly abused surveillance powers to monitor millions without court approval. Criminals actively target visible crypto holders, and high-profile kidnappings like David Balland (Ledger) and Dean Skurka (WonderFi) prove that public wealth makes you a target. Data brokers and hackers need just one breach at an exchange to expose your complete financial history. You're one leak away from becoming a target for all of them. Those are only a few of many reasons why privacy matters!
Or maybe you're already ahead of the curve. You followed the advice in How to Buy Crypto Anonymously (Part 1), bought Bitcoin or Ethereum anonymously, and now hold a wallet no one can link to your identity. No regulator can legally force disclosure of your transaction history. But how do you stay anonymous while transferring, trading, or participating in DeFi?
These are two different starting points. But the practice to stay private while using crypto is identical for both.
The moment you move coins, you leave permanent fingerprints on the blockchain. That 1 ETH you transfer every first of the month at 8 PM? That's not random. That's a signature.
Security without privacy makes you a well-protected sitting duck. Privacy without security means you're invisible but vulnerable, one phishing link away from losing everything. This post gives you the framework to turn both KYC-tainted and privately acquired crypto into anonymous holdings you can actually use. We'll focus on anonymizing your Bitcoin and Ethereum holdings, each with specific methods: Monero as a privacy layer for Bitcoin; for Ethereum, Railgun as a shielded environment, and Privacy Pools and Tornado Cash as mixers.
But before you jump in, you need a foundation. Chapter 1 outlines your Minimum Viable OpSec. If you're not operating at this level, every privacy tool you apply will be built on sand.
Let's get into it.
1. Minimum Viable OpSec
You are ready to use your crypto anonymously. But before you move a single coin, you must harden your foundation. This is not optional. One mistake now will permanently link your entire portfolio to your identity.
Think of your setup as built on two distinct pillars: Security and Privacy.
- Security is about protection. It ensures that mistakes or attacks do not result in permanent loss. It encompasses your wallet, keys, and recovery plan.
- Privacy is about obscurity. It prevents anyone from linking your financial activity to your identity in the first place.
Failing at security means you lose your coins. Failing at privacy means you become a visible target. You need both.
Your first task is to audit your operational security against the non-negotiable baseline. The complete Crypto OpSec Guide outlines level 1 to 3 for security and privacy. You do not need level 3 to start. But you must be operating at Level 1: The Essential Foundation.
Recap from the OpSec Guide: Your Non-Negotiable Level 1 Checklist
| Setup (do this once, now) | Procedure (do this every time) |
|---|---|
| Security | |
| - Use a hardware wallet (e.g. Trezor, Cypherock, Coldcard, BitBox02) and connect it with a privacy-focused desktop wallet (e.g. Sparrow for BTC, Frame for ETH) - Store a seed backup on paper/metal, separate from your hardware wallet (no digital copies) - Give a trusted person a sealed envelope with seed location (not the phrase) and recovery instructions |
- Verify every destination address on your hardware wallet screen before signing - Always send a trivial test transaction before moving large sums - Keep firmware/software updated from official sources only |
| Privacy | |
| - Never talk about your holdings, addresses, or transactions - Buy your hardware wallet anonymously via cash (never ship it to your home address) - Never reuse identifiers: Use unique, anonymous emails/usernames (Tuta/Proton) and avoid KYC checks whenever possible - Use a dedicated user account or machine for all crypto activities. Enable full disk encryption - Configure a strict no-log VPN (e.g., Mullvad) |
- Separate your wallets in KYC-PUBLIC & PRIVATE-ANON based on whether the wallet can theoretically be linked to your identity. Never send assets directly between a KYC and a private wallet - Verify environment: Confirm VPN is active and you are operating from your dedicated crypto account or machine before launching any wallet |
The methods in the next chapters assume your foundation is solid and you are not already compromised.
Complete the setup. Follow the procedure. Then, you are ready for the next step.
2. Bitcoin Anonymization
The Monero Pipeline
⚠️ OpSec Prerequisite
Your foundation determines your exposure. The methods below will not protect you if your operational base is weak. Every method assumes you have implemented the Minimum Viable OpSec. If you have not, stop here and implement it first. See the summary in Chapter 1 or the full Crypto OpSec Guide.
Scenario A: Non-KYC Holdings
If you acquired your Bitcoin anonymously via P2P exchanges or private purchases, there is no link between the coins and your identity.
- The Strategy: Do Nothing. Move the coins to your dedicated hardware wallet and let them sit. The blockchain records a transaction; your identity remains unlinked.
- Spending (services or goods): Never pay directly from your main wallet. Isolate the funds by sending a randomized amount to a burner wallet (hop once for future deniability), never the exact purchase sum. Then, your best path is to atomic swap to Monero and pay in XMR. Bitcoin exposes your history and balance to the merchant; Monero breaks the link to your Bitcoin holdings entirely.
Scenario B: KYC-Tainted Holdings
This is the "Contamination Zone." Your wallet is linked to your identity.
The Monero Pipeline
Everything on Bitcoin is permanently visible. You break the linkage by moving your funds to Monero, obfuscating them within the Monero environment, and returning them to new Bitcoin wallets. The diagram illustrates the architecture:
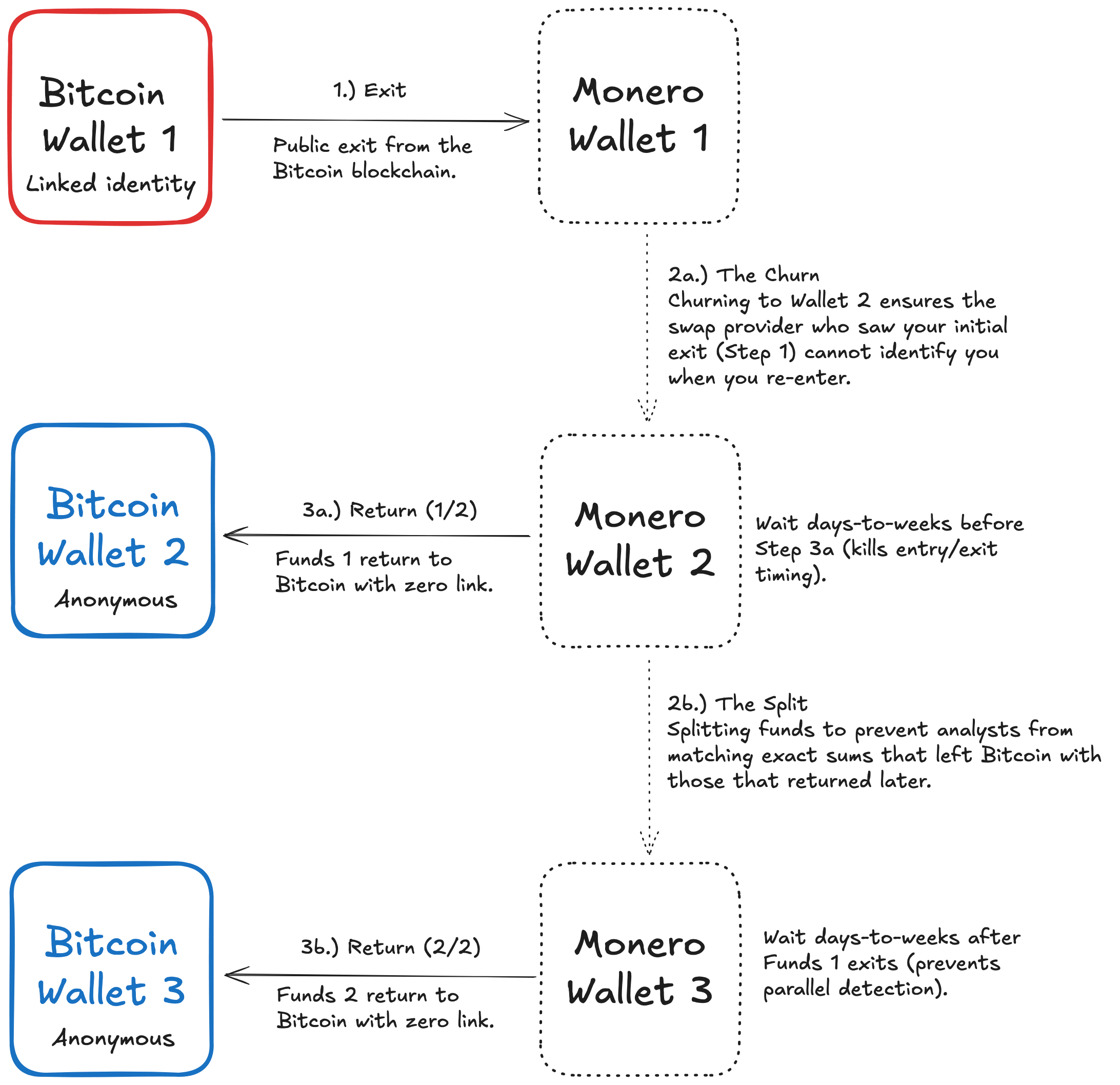
Graphics: The BTC Anonymization Pipeline
Operational Notes:
-
Time is a shield. Wait days, ideally weeks. Returning to Bitcoin hours after exiting creates temporal fingerprints that mathematics cannot obscure.
-
Close the metadata loophole. Execute the Churn and the Split correctly and you remain anonymous on the blockchain. Your only remaining exposure is potential honeypot coordinators. The service that facilitates your Exit logs your IP, browser fingerprint, and trade size. If you return to that same provider, or if the coordinators from Step 1 and Step 3 collude, they can correlate your Exit and Return using metadata alone.
How to avoid this: Use different tools for Exit and Return. Use different devices or fresh browser profiles. Never let the same infrastructure witness both legs of the journey. -
Bitcoin Wallet 2 and Bitcoin Wallet 3 are separate identities, not merely separate wallets. Treat them as belonging to strangers who have never met. Never merge funds in a future transaction. One violation collapses both anonymity sets instantly.
You can add more wallets to reduce the chance of amount correlation (matching exit and return sums) further, but consider the trade-off. Each additional wallet multiplies your OpSec attack surface and increases the risk of human error (accidental address reuse, synchronized timing, etc.).
Implementation
In this section we evaluate tools for these two critical steps in the pipeline: Step 1 (The Exit) converts tainted Bitcoin to private Monero, and Step 3 (The Return) brings clean Bitcoin back to new wallets.
Cross-Chain Atomic Swaps, P2P Marketplaces, and Haveno let you transfer Bitcoin and Monero without KYC, custody, or permission. They are designed to be as privacy-preserving as technically possible. Yet none of them provide anonymity on their own. These tools get you to Monero and back. Privacy comes from Monero plus your operational discipline.
While your funds are in Monero, ring signatures and stealth addresses obscure the trail. Your operational discipline (time delays, churning, splitting returns, and using different tools for Exit and Return) determines whether the entire pipeline remains untraceable.
1. Cross-Chain Atomic Swaps
Tools: Eigenwallet (formerly Unstoppable), BasicSwap
You trade directly with another person’s wallet using code-enforced contracts (HTLC/PTLC). No custody, no KYC, no permission required.
Privacy Assessment: The tools provide access, not privacy.
Atomic swaps are a permissionless bridge to Monero. They allow you to acquire XMR without intermediaries. But the swap itself does not anonymize your funds. The relay network sees your VPN or Tor exit IP, trade amount, and timing. The counterparty sees your source and destination addresses for that leg only. The on-chain Bitcoin trail remains visible up to the swap transaction.
Remaining Risk to Overall Privacy:
- Same-party correlation: If you use the same counterparty or relay network for both Exit and Return, they can correlate your activity through off-chain logs showing your IP, amounts, and timing. This is not blockchain analysis. It is metadata correlation. Mitigate by using different tools for each leg, splitting your return across multiple transactions, and using fresh Tor circuits.
- Global traffic analysis: A theoretical state-level threat if an adversary monitors all atomic swap relay networks simultaneously. Mitigate with multi-day or multi-week delays during the Churn.
| Metric | Rating | Details |
|---|---|---|
| Liquidity | 🔴 Low | Eigenwallet pools ~1.3 BTC for XMR (as of February 2026). |
| Ease of Use | 🟡 Medium | Eigenwallet: Good usability. Simple installer. BasicSwap: Low usability. ~60 min setup and Particl node sync. |
| Fees | 🟡 Medium - 🔴 High | Approx. 2-3% mark-up on each BTC/XMR transaction. |
Table: Cross-Chain Atomic Swaps rating
2. P2P Marketplaces
Tools: Bisq, RoboSats
Peer-to-peer marketplaces connect buyers and sellers directly. No custody, no KYC, permissionless access. But the platforms differ significantly in their on-chain footprint.
Tool-Specific Privacy Profiles:
- Bisq: Trades leave permanent, identifiable fingerprints on the Bitcoin blockchain. The BSQ token enables address clustering. Avoid it by paying fees in BTC instead. Research has demonstrated BSQ clustering attacks.
- RoboSats: Uses Lightning Network. Transactions are routed privately between nodes rather than recorded on the public blockchain. This leaves no permanent (but an ephemeral) trail for chain analysis, avoiding Bisq's fingerprinting issue.
Privacy Assessment: The tools provide access, not privacy.
Remaining Risk to Overall Privacy:
- Same-party correlation: If you use the same P2P platform for both Exit and Return, the coordinator can correlate your activity through off-chain logs. Mitigate by using different platforms for each leg, splitting your return, and using fresh Tor circuits.
- Bisq trade identification (inherent): Bisq transactions leave recognizable patterns on the Bitcoin blockchain.
- Bisq BSQ exposure (avoidable): The BSQ token enables address clustering that aggregates all DAO activity to a single identity. Avoid by paying fees in BTC and not participating in DAO governance.
- Dispute visibility: If arbitration is required, the arbitrator gains visibility into trade details and your ephemeral identity.
| Metric | Rating | Details |
|---|---|---|
| Liquidity | 🔴 Low - 🟡 Medium | 🟡 Bisq has medium XMR liquidity (<5 BTC up to 2% mark-up as of Feb 2026). 🔴 RoboSats has low liquidity (<1 BTC as of Feb 2026). |
| Ease of Use | 🟡 Medium | Bisq is a desktop client for advanced users. Robosats is web-based and easier to use, but requires Lightning wallet set-up. |
| Fees | 🟡 Medium | Bisq: 1.3% trading fee (0.15% maker, 1.15% taker) plus min. 0-2% mark-up. RoboSats: 0.2% (0.025% maker,0.175% taker) plus min. 0-1% mark-up. |
Table: P2P Marketplaces rating
3. Haveno Networks (Monero-Native DEX)
Networks: Retoswap
Haveno is open-source DEX software that anyone can deploy. Multiple independent networks operate on Haveno, each with its own arbitrators and liquidity. Retoswap is currently the largest. The software uses staked XMR bonds instead of BTC collateral. All connections run over Tor.
Privacy Assessment: The tool provides access, not privacy.
Haveno is built for privacy from the ground up. No proprietary token exists, eliminating Bisq's address clustering risk. All connections route through Tor by default. But the trade itself does not anonymize your funds.
The federated seed nodes see your Tor exit IP, timing, and trade parameters. They cannot link your on-chain activity directly, but they retain metadata that could be correlated. Arbitrators see full transaction details only during disputes.
Remaining Risk to Overall Privacy:
- Same-party correlation: If you use the same Haveno network for both Exit and Return, its federated nodes can correlate your activity through off-chain logs. Mitigate by using Haveno for only one leg and a different tool for the other, splitting your return, and using fresh Tor circuits.
- Arbitrator exposure: Disputes reveal transaction details to the selected arbitrator.
- Bond visibility: Your XMR security deposits and releases are visible to the federated arbitration system.
| Metric | Rating | Details |
|---|---|---|
| Liquidity | 🟡 Medium | Approx. 3 BTC liquidity in the 2% mark-up spread as of Feb 2026. |
| Ease of Use | 🟡 Medium | Desktop application with Tor sync. Requires XMR security deposit unless using no-deposit offers. |
| Fees | 🟡 Medium - 🔴 High | Trading fees: 0.1-1% depending on role and payment type. Additionally, approx. 2% mark-up on. |
Table: Haveno Networks rating
4. Centralized Exchanges (CEX)
Tool: Kraken
Regulated exchange requiring full KYC. Deep liquidity pools.
The only viable path is to use a CEX (Kraken) one-way for the Exit (step 1: acquiring Monero), but not for the Return (step 3).
Privacy Assessment: CEX provide liquidity and low transaction fees, not privacy.
A CEX is the opposite of permissionless. Full KYC permanently links your real-world identity to every transaction. Internal records associate your name, address, and government ID with the Monero withdrawal address. The Monero blockchain obscures subsequent activity from public view, but the exchange retains the link between your identity and your XMR acquisition.
A CEX is viable only for the Exit, never for the Return due to KYC.
Remaining Risk to Overall Privacy:
- Permanent surveillance: Internal records permanently associate your real-world identity with the Monero acquisition and withdrawal address.
- State exposure: Complete transaction transparency to government entities.
- Data breach: Centralized KYC databases are high-value targets for identity theft and targeted attacks.
| Metric | Rating | Details |
|---|---|---|
| Liquidity | 🟢 High | Unmatched. Deep pools capable of swallowing massive amounts of capital. |
| Ease of Use | 🟢 High | Familiar, polished interfaces. Easy to navigate. |
| Fees | 🟢 Low | Maker fees: Range from 0-0.25%. Taker fees: Range from 0.1-0.4%. |
Table: CEX rating
Operational Discipline Across All Tools
The main threat above is same-party correlation and has a common mitigation: Use different tools for Exit and Return. Never let the same platform, coordinator, or relay network witness both legs of your pipeline. Wait days, ideally weeks during the Churn to minimize odds for correlation. Split your return across multiple wallets to break amount-matching heuristics. Use fresh Tor circuits or VPN endpoints for each transaction. The on-chain trail is broken by Monero; metadata correlation across time, tools, and amounts is the remaining theoretical threat. Your operational discipline creates the necessary obfuscation.
⚠️ Warning on Instant Swappers: Services like ChangeNOW, SimpleSwap, Godex, and StealthEX appear on getmonero.org and market themselves as "no KYC." All four services explicitly reserve the right to freeze funds and demand identity verification at any time. Users report funds locked for weeks and withheld even after providing documentation. These services are not recommended for the Monero Pipeline. The freezing risk defeats the purpose of anonymous transactions. Use Atomic Swaps, P2P Marketplaces, or Haveno instead.
💡Note on On‑Chain Mixing: CoinJoin and similar services obfuscate Bitcoin trails without converting to Monero. While feasible for minor privacy improvements, they require trusting a coordinator (vulnerable to logging or honeypot compromise). CoinJoin breaks the link from casual observers but offers no certain privacy against state‑level actors with coordinator visibility. Other mixer services like JoinMarket have fundamental flaws, too. For highest privacy requirements, the Monero Pipeline remains superior. Peter Todd wrote a detailed analysis on Bitcoin mixing services.
3. Ethereum Anonymization
Privacy without leaving Ethereum
⚠️ OpSec Prerequisite
Your foundation determines your exposure. The methods below will not protect you if your operational base is weak. Every method assumes you have implemented the Minimum Viable OpSec. If you have not, stop here and implement it first. See the summary in Chapter 1 or the full Crypto OpSec Guide.
3.1 Non-KYC Holdings
If you acquired ETH anonymously via P2P exchanges or private purchases and hold it in a new wallet, there is no link to your identity. Skip the anonymization process described in the next section 3.2 entirely and move the assets to your dedicated hardware wallet.
If you intend to actively participate in DeFi (swaps, lending, yield farming), you may optionally shield the funds into Railgun to obscure your strategies from front-running bots and competitive observers.
3.2 KYC-Tainted Holdings
The Monero Pipeline to anonymize Bitcoin from chapter 2 works similarly for Ethereum: atomic swap to XMR, churn, and return to new Ethereum wallets. However, Ethereum's programmability enables a native alternative: shielded pools.
Instead of switching the blockchain, deposit KYC-tainted ETH into a zero-knowledge smart contract. Assets commingle under cryptographic guarantee. You withdraw to new addresses with zero blockchain link. You can optionally participate in DeFi while remaining shielded.
3.2.1 Railgun
Railgun is a non-custodial, on-chain privacy protocol using zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) to shield token transfers, swaps, lending, and dApp calls. It allows (1) anonymization of ETH holdings by breaking the on-chain link between old and new wallets, and (2) private DeFi interaction without exiting the shielded environment.
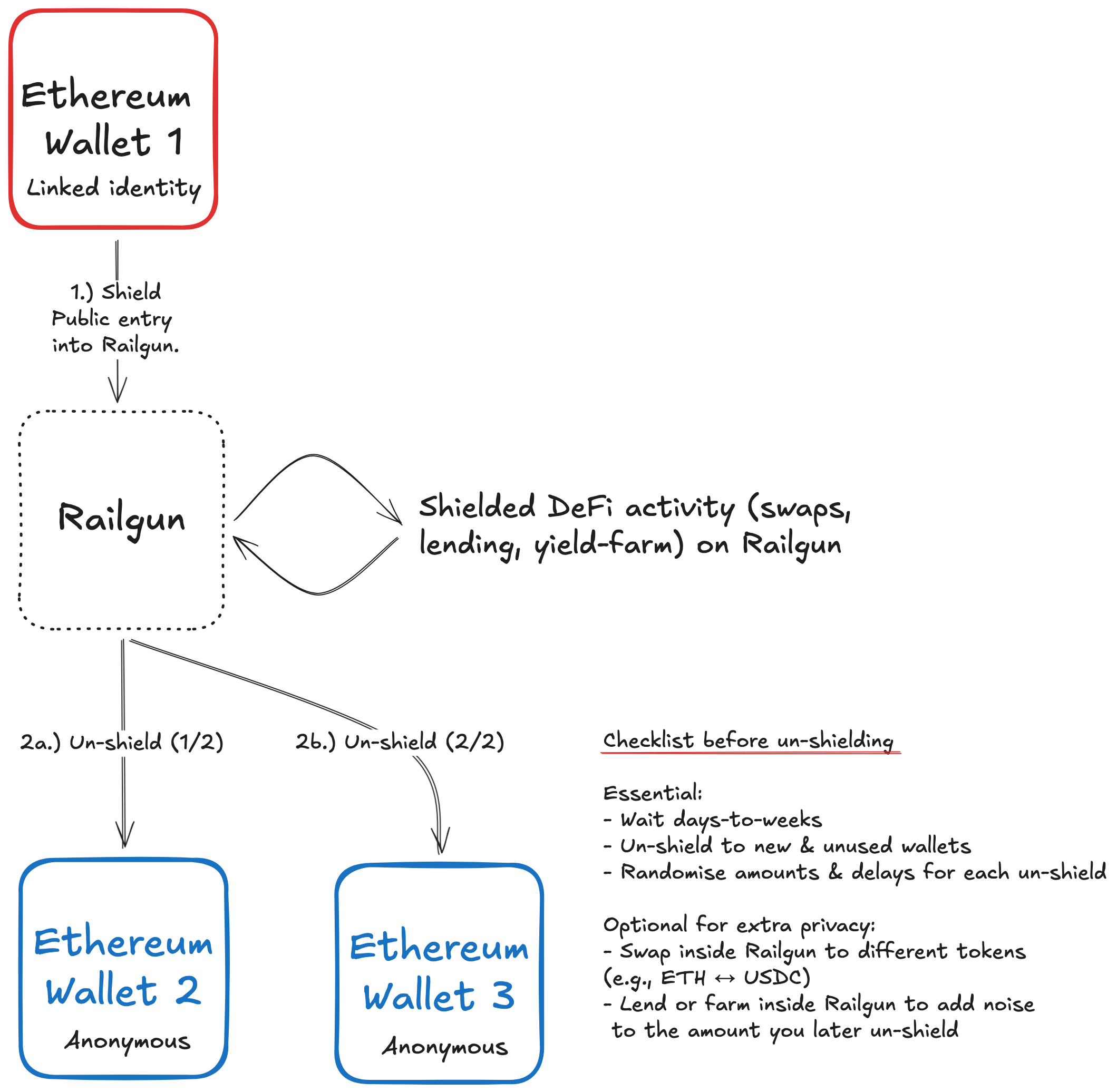
Graphics: The Railgun anonymization process
Privacy Assessment: High. Railgun achieves this through zk-SNARK shielding that hides amounts, token types, and sender and receiver addresses from all blockchain observers. A decentralized relayer network breaks gas-payer heuristics by allowing third parties to submit proofs on your behalf, preventing correlation between your Ethereum address and your shielded activity. The substantial anonymity set of approximately $36m in shielded ETH volume (as of Feb 2026) makes deposit-to-withdrawal correlation statistically difficult, as each withdrawal is drawn from the entire pool rather than your specific deposit.
Other Features:
- Private Proofs of Innocence: A decentralized system that automatically generates a zero-knowledge proof verifying that shielded tokens do not appear on public blacklists. This allows you to prove funds are clean to counterparties without revealing address, balance, or transaction history.
- Private DeFi: Within a shield you can swap ETH, lend/borrow, provide liquidity, interact with NFTs or other dApps, and bridge to other compatible chains, all with inputs and outcomes hidden from public blockchain explorers.
Remaining Risks:
- Contract upgrade risk: DAO-governed parameters mean malicious upgrades could theoretically freeze or expose funds if governance is compromised.
- Missing hardware wallet support: No Railgun-compatible wallet (including Railway and Terminal) currently supports native hardware wallet integration. You must manage private keys in hot wallet environments, increasing exposure to device compromise compared to air-gapped or hardware security module storage.
- Relayer logging: Relayers could log IP metadata. Mitigate with Tor/VPN or privacy-focused proxies when generating proofs.
- Viewing-key exposure: Never use or share the viewing key. Although it exists to share info with third parties like your accountant, handing it out nullifies the anonymity you are after.
| Metric | Rating | Details |
|---|---|---|
| Privacy | 🟢 High | zk-SNARKs hide amounts and addresses; decentralized relayers prevent correlation; ~$36m anonymity set. Non-custodial. |
| Liquidity | 🟢 High | Deep pools for ETH, USDT, DAI and USDC. Check pool sizes on Etherscan. |
| Ease of Use | 🟡 Medium | Requires separate wallet. You need to understand shield/un-shield mechanics and using relayers. |
| Fees | 🟡 Medium | 0.25% for shielding and 0.25% for un-shielding. |
Table: Railgun rating
3.2.2 Privacy Pools
Privacy Pools is an on-chain mixer and Tornado Cash fork, adding a compliance screening system that checks deposits against compliance lists to avoid that illegal funds enter Privacy Pools. You deposit your KYC-tainted ETH, pass verification, and withdraw to a new address with zero blockchain link.
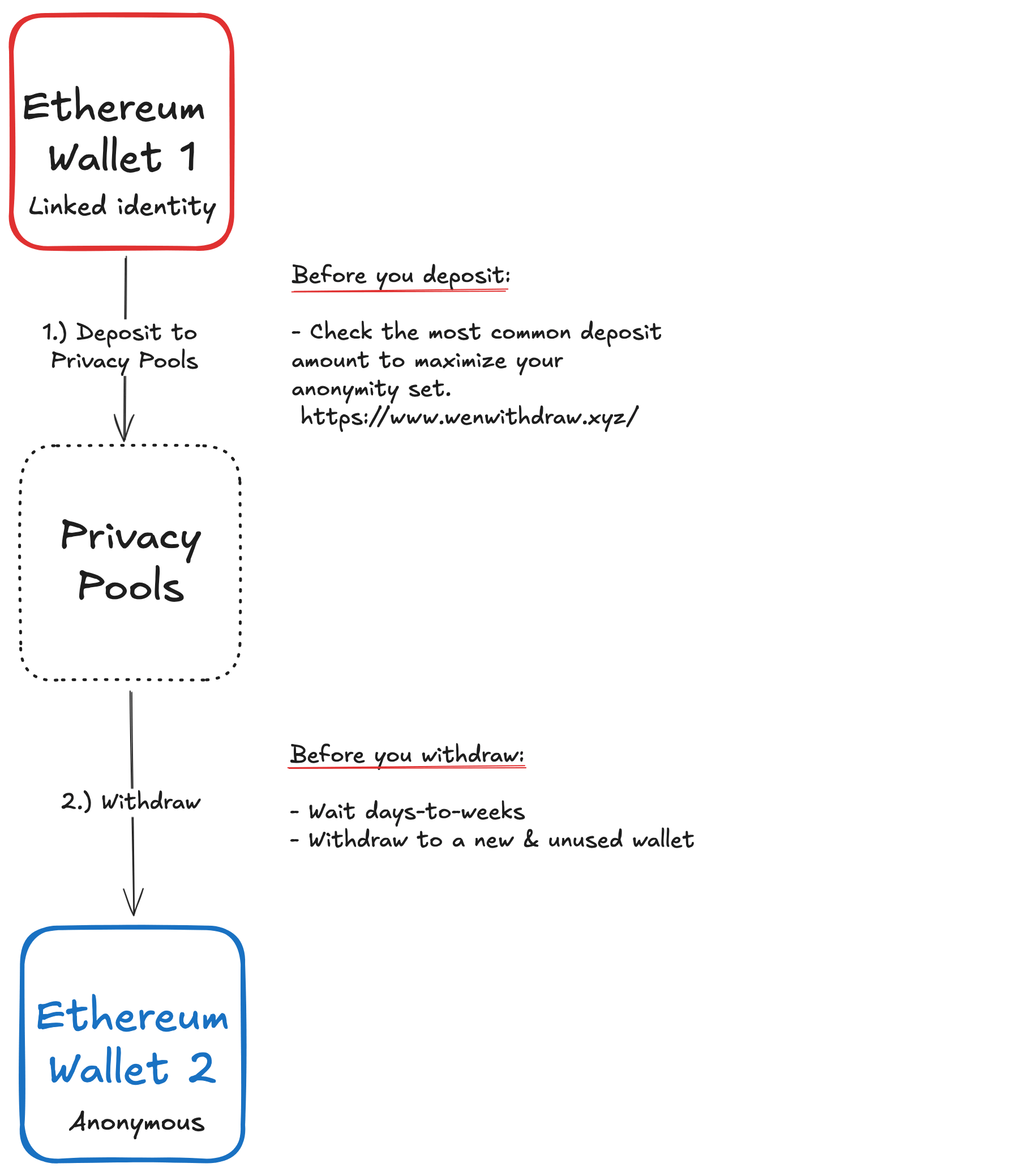
Graphics: The Privacy Pools anonymization process
Privacy Assessment: Medium. Privacy Pools uses zk-SNARK shielding. The primary limitation is a smaller anonymity set compared to Railgun, which increases amount correlation risk. Chain analysis can more easily match deposits to withdrawals by transaction size. Mitigate this by using pools with the highest deposit volumes, choosing a deposit & withdraw amount that is most common and adding a randomized wait time (days, not hours) between deposit and withdrawal.
Other Features:
- Compliance verification: Automated screening blocks funds linked to known criminal activity. Keeping them out of the pool reduces your risk of future complications.
Remaining Risks:
- Contract upgrade risk: DAO-governed parameters mean malicious upgrades could theoretically freeze or expose funds if governance is compromised.
- Single curator censorship: One entity controls access and can deny deposits for any reason, error, legal pressure, or policy change. If denied, funds return to your source wallet via Ragequit. You do not risk losing your coins, but you might get denied access to Privacy Pools.
- Metadata exposure: Single curator infrastructure or relayers could log IP metadata. Mitigate with Tor/VPN and changing connection patterns.
| Metric | Rating | Details |
|---|---|---|
| Privacy | 🟡 Medium | zk-SNARKs hide deposit-withdrawal links. Smaller anonymity set increases amount correlation risk. Non-custodial. |
| Liquidity | 🟡 Medium | As of February 2026: Only the ETH pool has significant liquidity ($1.5m). Others are thin. Railgun's ETH pool is considerably larger at $36m. |
| Ease of Use | 🟢 High | Simple web UI with standard wallet and hardware wallet support. |
| Fees | 🟡 Medium | Deposit fee of 0.5% (no withdrawal fee). |
Table: Privacy Pools rating
3.2.3 Tornado Cash
Tornado Cash is an on-chain mixer and the closest it gets to cypherpunk principles: permissionless, immutable, decentralized, open-source, censorship resistant, and private.
Its purity made it irresistible to criminals. North Korea’s Lazarus Group laundered billions through it. Regulators struck back in August 2022, when the U.S. Treasury sanctioned the protocol, criminalizing American usage and arresting its developers.
Then, in March 2025, the courts forced a delisting of Tornado Cash. The code is legal again. But the composition of its anonymity set is unchanged, with a significant portion of illegally acquired funds mixed in.
Here is the complication: When you use Tornado Cash as a good actor, you mix your funds in the same cryptographic pool with criminal funds. Afterwards, you should not use centralized platforms or centralized tokens (like USDT or USDC) again, as this creates identification risk or even freezes down the road.
That is why Tornado Cash only makes sense if these four priorities outweigh any complexity risk down the line:
- Maximum anonymity set: You need the deepest liquidity pool (as of February 2026 more than $400m) and accept that exchanges may flag your funds.
- Censorship resistance: You are a journalist or whistleblower in a hostile regime who cannot risk a curator blocking your deposit. Only immutable code guarantees access.
- No regulated future: You use anonymous on- and off-ramps for the fiat system or even permanently exited fiat.
- Pure ideology: You prioritize protocol decentralization over compliance. You demand that privacy tools must not discriminate between users.
If these four conditions matter more to you than future friction, use Tornado Cash. Otherwise, use Railgun or Privacy Pools to maintain proof of innocence when passing compliance checks.
| Metric | Rating | Details |
|---|---|---|
| Privacy | 🟢 High | zk-SNARKs. Largest anonymity set ($400m+). Immutable, Trustless. Big "but": mixes with illicit funds. |
| Liquidity | 🟢 High | Deep liquidity with $400m+ total pool volume. Check different pool sizes in the Tornado Cash UI. |
| Ease of Use | 🟢 High | Simple deposit/withdraw. No verification required. Hardware wallet support. |
| Fees | 🟡 Medium | 0.3% per withdrawal. Lowest fees among the three options. |
Table: Tornado Cash rating
3.2.4 Verdict
Railgun, Privacy Pools, and Tornado Cash are non-custodial, on-chain tools to anonymize funds, but they serve different profiles.
Railgun is a full privacy platform. Shielded addresses enable private DeFi, including swaps, lending, and yield, without creating on-chain links. Fees total 0.5% (0.25% each for shielding and un-shielding). Anonymity sets are substantial (ETH shielded volume: $36m) and increase through ongoing DeFi activity. Proof of Innocence lets you demonstrate clean funds without revealing history.
Privacy Pools is a mixer focused breaking the on-chain link while keeping illicit funds out of the pool. Simple web UI, hardware wallet support, 0.5% entry fee. The trade-off is a smaller anonymity set ($1.5m), which increases amount correlation risk compared to Railgun or Tornado Cash.
Tornado Cash is the purest mixer: immutable, permissionless, censorship-resistant. It offers the largest anonymity set (pool volume: $400m+) and lowest fees (0.3% per withdrawal). The trade-off is final: By (probably) mixing with illicit funds, you permanently detach from regulated systems. No centralized exchanges. No centralized coins like USDT or USDC. Exiting to fiat requires private off-ramps.
Recommendation:
For most good actors, Railgun balances privacy, utility, and compliance. For simple one-time anonymization, Privacy Pools offers the easiest user experience. For those who prioritize pure cryptographic privacy above all and accept permanent detachment from regulated finance, Tornado Cash remains the cypherpunk standard.
4. Execution Playbooks
From Theory to Execution
Anonymizing Bitcoin and Ethereum is not trivial. We covered strategies and tools. Each tool has its own strengths, and trade-offs. Each strategy requires disciplined execution.
In this chapter, we'll walk through two concrete scenarios. Two complete playbooks. Each starts with KYC-tainted funds on a CEX and ends with anonymous wallets. Follow them or adapt them.
4.1 Playbook: Anonymizing 3 BTC
Starting point: 3 BTC on Kraken (KYC-linked) → Goal: 2 isolated, anonymous Bitcoin wallets
Parameters:
- Duration: 4 weeks
- Privacy Level: High
- Effort: High
- Fee Cost: ~0.135-0.15 BTC (4.5-5%), comprising Exit (Eigenwallet: ~2% markup plus network fees) and Return (Retoswap: ~2.5% in fees plus network fees)
- Exit Tool: Eigenwallet (Atomic Swaps)
- Return Tool: Retoswap (Haveno)
⚠️ Transaction Hygiene
- Test transaction: Always send a trivial test transaction (0.001 BTC) before moving full amounts. Do this for all transactions including swaps, and P2P trades.
- Hardware verification: Confirm all destination addresses on your hardware wallet screen, never just on your monitor.
- Consistency: Apply this protocol to every single transaction in this playbook.
Execution timeline:
| Phase | Timeline | Action |
|---|---|---|
| Setup | Day 1-7 (complete at your own pace) |
1. Create a dedicated OS user account (ideally on a dedicated machine). Disable all telemetry. 2. Install: Mullvad VPN (activate kill-switch), Brave (hardened), Sparrow Wallet, Eigenwallet, Monero GUI Wallet, Trezor Suite. 3. Buy a Trezor Safe 3 in cash (Best Buy in US; full reseller list). 4. Set up your Trezor Safe 3 using Trezor Suite. Update the firmware. Generate your seed on your Trezor Safe 3 device. The device will display the 24-word phrase. Write it down on paper or metal (never digital). 5. In Sparrow, connect your Trezor as a hardware wallet. Create a fresh wallet address derived from your Trezor seed and label it KYC_Sparrow_BTC_1.6. In Monero GUI Wallet, generate a new wallet. Create two subaddresses and label them Temp_MoneroGUI_XMR_1 andTemp_MoneroGUI_XMR_2. Write down the seed phrase on paperor metal (never digital). Trezor Safe 3 works with Monero GUI. 7. Give a trusted person a sealed envelope with seed location (not the phrase) and recovery instructions. 8. Withdraw 3 BTC from Kraken to KYC_Sparrow_BTC_1.First and only reminder: Transaction hygiene! |
| Exit and Churn |
Day 8-12 | 1. Connect Mullvad VPN. Verify kill-switch is active. 2. In Eigenwallet, create a BTC address and label it KYC_Eigenwallet_BTC_1. Create a Monero subaddress and labelit Temp_Eigenwallet_XMR_1. Security note: Eigenwallet is a hotwallet. Keys exist on your device. 3. Transfer 3 BTC from KYC_Sparrow_BTC_1 to KYC_Eigenwallet_BTC_1.4. Execute atomic swaps in batches based on available liquidity. Example split: 0.5 BTC → XMR, 1.0 BTC → XMR, 1.5 BTC → XMR. Each swap incurs ~2% markup plus network fees. 5. Transfer received XMR from Temp_Eigenwallet_XMR_1 toTemp_MoneroGUI_XMR_1 and Temp_MoneroGUI_XMR_2 (splitapproximately evenly). Result: XMR equivalent to ~1.5 BTC in each Monero GUI wallet. The on-chain trail now ends at Monero's ring signatures. |
| Wait | Day 12-18 | Let time create distance. Patience is operational security. A rushed return creates temporal fingerprints that algorithms can correlate. |
| The Split | Day 18 | Your exit split ~1.5 BTC equivalent into each Monero wallet. That symmetry is a correlation vector. Break it: From Temp_MoneroGUI_XMR_1, send 0.5 BTC equivalent toTemp_MoneroGUI_XMR_2.Result: ~1 BTC equivalent in Temp_MoneroGUI_XMR_1 and~2 BTC equivalent in Temp_MoneroGUI_XMR_2. Amount correlation broken. |
| Return 1 | Day 18 | 1. In Sparrow, generate a fresh wallet address. Label itPRIVATE_Sparrow_BTC_1.2. Connect to Retoswap (Haveno). Under "Cryptocurrency accounts," add PRIVATE_Sparrow_BTC_1 as your BTC destination address.3. Go to "Sell XMR" → "Sell XMR for Crypto" → "BTC". Expect ~2.5% in fees (2% markup + 0.5% taker fee) plus network fees. 4. Transfer ~1 BTC worth of XMR from Temp_MoneroGUI_XMR_1to the displayed trade wallet address. Result: ~1 BTC in PRIVATE_Sparrow_BTC_1. No blockchain linkto your Kraken origin. |
| Wait | Day 19-20 | Maintain temporal separation between Return 1 and Return 2. Minimum 48-72 hours. |
| Return 2 | Day 21 | 1. In Sparrow, generate a fresh wallet address. Label itPRIVATE_Sparrow_BTC_2.2. Connect to Retoswap with a fresh Tor circuit. Under "Cryptocurrency accounts," add a new account with PRIVATE_Sparrow_BTC_2 as your BTC destination address.3. Go to "Sell XMR" → "Sell XMR for Crypto" → "BTC". Expect ~2.5% in fees plus network fees. 4. Transfer XMR from Temp_MoneroGUI_XMR_2 to the displayedtrade wallet address. Split across multiple trades if needed. Result: ~2 BTC in PRIVATE_Sparrow_BTC_2. Temporal and amountseparation from Return 1. No blockchain link to your identity. |
Wallet Overview
| Wallet | Purpose |
|---|---|
KYC_Sparrow_BTC_1 |
Initial Kraken withdrawal. Archive and never reuse. |
KYC_Eigenwallet_BTC_1 |
Exit-phase temporary. Clear data after use. |
Temp_MoneroGUI_XMR_1 |
Churn + Return source. Clear data after use. |
Temp_MoneroGUI_XMR_2 |
Churn + Return source. Clear data after use. |
PRIVATE_Sparrow_BTC_1 |
Final anonymous wallet. Your first clean identity. |
PRIVATE_Sparrow_BTC_2 |
Final anonymous wallet. Your second clean identity. |
Key OpSec Reminders
- Never merge funds between
PRIVATE_Sparrow_BTC_1andPRIVATE_Sparrow_BTC_2. They are legally separate entities in your mental model. - Spending discipline: When paying for goods or services, never send directly from
PRIVATE_Sparrow_BTC_1/2. First send to a temp BTC wallet (for deniability) and then atomic swap to Monero and pay in XMR. - Future acquisitions: If you buy more Bitcoin later, never send it to
PRIVATE_Sparrow_BTC_1orPRIVATE_Sparrow_BTC_2. Repeat the process with a newly generatedPRIVATE_Sparrow_BTC_3wallet.
Your 3 BTC is now anonymized. Two clean wallets. No blockchain link to your identity remains. The trail ends at Monero's ring signatures.
Main threat vector: amount and time correlation
A sophisticated state-level adversary could theoretically correlate your 3 BTC exit with two subsequent returns totaling the same amount within a narrow time window. Monero's privacy architecture provides strong protection, but these measures further reduce risk:
- Split across more wallets: Return to 3-4 wallets instead of 2. Each additional address reduces correlation probability.
- Leave funds in Monero: Keep 5-10% of your XMR in Monero rather than returning the full amount. This breaks precise amount matching between exit and return.
- Add noise during the wait: Receive XMR from an independent source (a friend, a separate purchase) during the churn period. Mix it with your holdings before return. The return amount will differ measurably from the exit, defeating amount correlation.
- Use different tools for the return leg: Your playbook uses Retoswap for both Return 1 and Return 2. For maximum privacy, use different tools for each return. Example: Retoswap for Return 1, Eigenwallet for Return 2. No single coordinator can correlate your full activity.
For highest privacy, combine at least three of these measures.
4.2 Playbook: Anonymizing 100 ETH
Starting point: 100 ETH on Coinbase (KYC-linked) → Goal: 2 isolated, anonymous Ethereum wallets
Parameters:
- Duration: 2-3 weeks
- Privacy Level: High
- Effort: Medium
- Fee Cost: ~0.5 ETH (0.25% shielding fee + 0.25% un-shielding fee) plus relayer and gas fees
- Tool: Railgun
⚠️ Transaction Hygiene
- Test transaction: Always send a trivial test transaction (0.0001 ETH) before moving full amounts. Do this for all transactions including swaps, and P2P trades.
- Hardware verification: Confirm all destination addresses on your Hardware Wallet screen, never just on your monitor.
- Consistency: Apply this protocol to every single transaction in this playbook.
Execution timeline:
| Phase | Timeline | Action |
|---|---|---|
| Setup | Day 1-7 (complete at your own pace) |
1. Create a dedicated OS user account (ideally on a dedicated machine). Disable all telemetry. 2. Install: Mullvad VPN (activate kill-switch), Brave (hardened), Frame wallet, Railway wallet, Trezor Suite. 3. Buy a Trezor Safe 3 in cash (Best Buy in US; full reseller list). 4. Set up your Trezor Safe 3 using Trezor Suite. Update the firmware. Generate your seed on your Trezor Safe 3 device. The device will display the 24-word phrase. Write it down on paper or metal (never digital). 5. In Frame, connect your Trezor as a hardware wallet. Create the following accounts, each derived from your Trezor seed: - Account 0: Label it KYC_Frame_ETH_1- Account 1: Label it PRIVATE_Frame_ETH_1 (for later use)- Account 2: Label it PRIVATE_Frame_ETH_2 (for later use)6. In Railway Wallet, generate another fresh wallet address and label it KYC_Railway_ETH_1. Security note: Railway does notsupport hardware wallets. Your keys will temporarily exist on this device. This is a trade-off for Railgun's native interface. 7. Backup your Trezor seed and Railway seed on paper or metal. Never store digitally. 8. Give a trusted person a sealed envelope with seed location (not the phrase) and recovery instructions. 9. Withdraw 100 ETH from Coinbase to KYC_Frame_ETH_1.First and only reminder: Transaction hygiene! |
| Hop for Deniability |
Day 8 | Transfer 100 ETH from KYC_Frame_ETH_1 to KYC_Railway_ETH_1. This hop gives legal deniability: If questioned, you can claim the transfer was unauthorized (hacked device, stolen seed, or phishing). The on-chain trail remains visible, but plausible legal alternatives exist. |
| Shield | Day 9 | 1. Connect Mullvad VPN. Verify kill-switch is active. 2. Execute a test shield of 0.01 ETH. Wait approximately 1 hour for the Proof of Innocence to generate. 3. Shield the remaining ~99.9 ETH. Result: ~99.75 ETH is now in your shielded balance (0.25% shielding fee deducted). |
| Decision Point |
Day 9-14 | You now have two options: A) Stay shielded: Keep funds in the shielded environment and access private DeFi (swaps, lending, yield). This adds noise to the anonymity set and maximizes privacy. You only un-shield when you want to sell or readjust your portfolio. B) Un-shield to fresh wallets: Withdraw to new addresses for full DeFi access on the public chain. We proceed with Option B in this playbook. |
| Wait | Day 9-14 | Let time create distance. A rushed un-shield creates temporal fingerprints. |
| Un-shield 1 | Day 15 | Un-shield your first batch (recommendation: 10-40 ETH) toPRIVATE_Frame_ETH_1.Result: ~10-40 ETH in your first clean wallet with no on-chain link to your Coinbase origin. |
| Wait | Day 16-18 | Maintain temporal separation. Randomize the exact timing. |
| Un-shield 2 | Day 19 | Un-shield the remaining ETH (approximately 60-90 ETH) toPRIVATE_Frame_ETH_2.Result: Your initial 100 ETH is now split between PRIVATE_Frame_ETH_1 and PRIVATE_Frame_ETH_2. Both walletshave no on-chain link to your identity or to each other. |
Key OpSec Reminders:
- Never merge funds between
PRIVATE_Frame_ETH_1andPRIVATE_Frame_ETH_2. They represent separate identities. Any on-chain interaction between them creates a permanent, publicly visible link. - Spending discipline: When paying for goods or services, never send directly from
PRIVATE_Frame_ETH_1/PRIVATE_Frame_ETH_2. First send to a temp ETH wallet (for deniability) and then atomic swap to Monero and pay in XMR. - Future acquisitions: If you acquire more Ethereum later, never send it to
PRIVATE_Frame_ETH_1orPRIVATE_Frame_ETH_2. Repeat the Railgun process with a newly generated wallet (e.g.,PRIVATE_Frame_ETH_3).
Your 100 ETH is now anonymized. Two clean wallets. No blockchain link to your identity remains. The trail ends at Railgun's zero-knowledge proofs.
Main threat vector: amount and time correlation
A sophisticated state-level adversary could theoretically correlate your 100 ETH shield with two subsequent un-shields totaling the same amount within a narrow time window. Railgun's anonymity set (~$36m) provides strong statistical protection, but these measures further reduce risk:
- Split across more wallets: Un-shield to 3-4 wallets instead of 2. Each additional address reduces correlation probability.
- Leave funds shielded: Keep 5-10% of your ETH in the shielded pool and use it for private DeFi activity. This adds noise and breaks precise amount matching.
- Vary your timing: Extend the playbook beyond 2 weeks. A 4-week timeline with randomized un-shield intervals significantly reduces temporal correlation.
- Add noise transactions: Execute small shield/un-shield cycles with independent amounts during the waiting period. This creates false patterns for any observer attempting correlation.
For highest privacy, combine at least three of these measures.
Inaction Is a Decision
The tools exist to anonymize your Bitcoin and Ethereum holdings. Rely on Monero's ring signatures and Railgun's zk-SNARKs. Use atomic swaps for cross chain transfers. None are perfect. All require discipline. But the alternative is permanently broadcasting your wealth to every scammer, criminal, data broker, and government agency. That is not an alternative at all. Not if you want to sleep well.
The playbooks in this article are not the only way. They are one way. Adapt them to your threat model. But whatever you do, do something. Because on a transparent blockchain, inaction is itself a decision. And that decision is: Everyone gets to watch, and you pay for the consequences.
Cassius Nox
Questions, ideas, or feedback? Reach me at cassius.nox@tuta.com.
